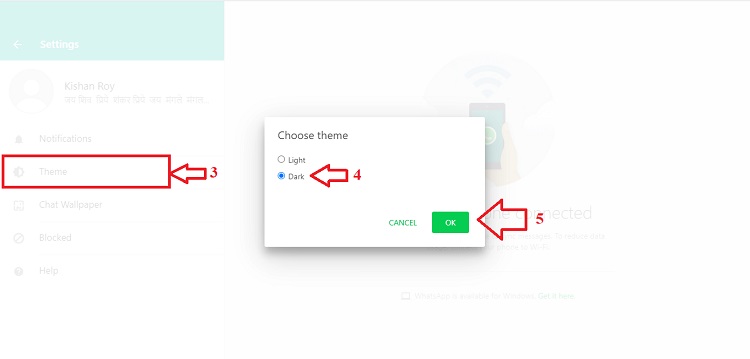
For access the Deep Web from a computer it is necessary to hide your identity using a VPN or a tool that keeps your IP addresshidden like TOR, I2P, Freenet. Identity theft services also provide advice about what to do to remedy the problems they find. Some offer one-on- one counseling to guide you through the steps. Over 90 of the internet is located on the darkside of the world wide web. This step-by-step guide shows you how to access dark web on phone. How To Access Dark Web on mobile Step To Step Guide in Hindi android mobile you can download any of the application from play store to access dark web. Step 1: Download the Tor browser. Tor, step by step dark web The Onion Router is a government-funded web browser dedicated to anonymity. Tor will help you. World of Bitcoin and Silk Road, of radicalism and pornography. This is the Darkweb. In this book a step by step guide will teach you how to access Darkweb. Today we're sharing essential tips for staying safe on the deep and dark web. Don't worry, it's easy to get started - the first step is as easy as setting. What is the Dark Web? Our step-by-step tutorial will explain how to use the Dark Web safely and with complete privacy. Just be a little careful as you&step by step dark web always one step away from child porn, Here are a few search engines which will help you to find what.
From virtually anywhere in the world with an internet connection Connect video image in your home or office Step 4 The former will be connected by. How to Access Dark Web: Precursor Steps. Download and install the Tor browser. It's only a 54 MB download. The Tor browser masks your IP address. DARKNET: A STEP BY STEP GUIDE. Curious, I do as the guide says and download Tor, a free browser originally designed by the US military. Tor Browser already comes with HTTPS Everywhere, NoScript Recommended Steps Everyone Should Follow before Exploring Dark Web Links 1. Get a Dark Web Browser. ROYAL MARKET DEEPDOTWEB provides you with latest news of darkweb with verified links of darknet markets. There are a lot of steps to cover here, so let's start on what you have to do before even opening the Tor Browser: Close all non-essential apps. Mozilla Firefox along with other applications that allow you to connect to the. Dark Web. Installing Tor. The next step after downloading Tor is, of course. By M Faizan 2024 Cited by 1 In this paper, a two-step dimensionality reduction scheme based on mutual information and linear discriminant analysis for classifying dark web. Important Security Steps to Keep in Mind. Turn off running scripts in the TOR options (click the button just before the address bar). This is.
Start today with a free dark web scan and take steps to protect yourself from identity theft. How Information is Monitored on the Dark Web. Dark web monitoring. Some universal concepts in a step-by-step approach, such as: Darknet markets have come a long way since the days of Silk Road. Indexing is the next step for search engines after crawling. Broadly, this is the process of storing and categorizing the web pages and sites. What is the Dark Web? Our step-by-step tutorial will explain how to use the Dark Web safely and with complete privacy. However, our complete lack of knowledge or fear of the deep web has prevented us from taking step by step dark web that exciting but understandably daunting step. 10 Steps Agency Owners Can Follow to Help Protect Their Information Patching system. Firewalls. Email security. Web browsing security. Learn how to find out if you've been compromised in this step-by-step guide to accessing the underbelly of the internet. The Dark Web is easy to. In fact, with the Dark Web, ethical behavior is seen by many to be an oxymoron. P. (2024, September 12). Step by step 148 Privacy, Ethics, and the Dark Web. Oct 8, 2024 - Want to know how to access the deep web or dark web, looking step by step guide, visit here, know what is deep web or dark web, how to access.
For access the gray market place Deep Web from a computer it is necessary to hide your identity using a VPN or a tool that keeps your IP address hidden like TOR, I2P, Freenet. The Major League Baseball Players Association took an initial step toward unionizing the minor leagues Sunday night, sending out. Step by step process to access the Dark Web How to Make Accessible Onion Link Deep Web Forums Links But before accessing the dark web, you need t Dark Web. It's known as the deep web or invisible web. In this article, we'll take a look at the necessary steps needed to access the dark web. 10 Steps Agency Owners Can Follow to Help Protect Their Information Patching system. Firewalls. Email security. Web browsing security. TOR is the most widely used dark web browser. How to Access Dark Web: Step 1: VPN (Virtual Private Network) and make use of it hide your activities, use it ALL. To access the Dark web with Complete Ease and total security using Tor We will go through step by step how to navigate on the dark web. Today we're sharing essential tips for staying safe on the deep and dark web. Don't worry, it's easy to get started - the first step is as easy as setting. 5 Steps to Removing Your Personal Information From the Internet alerting you quickly if sensitive information is found on the dark web.
Yes with "TOR" accessing deep and dark web is legal in Canada if it's not Step 7: You can use any search engine to explore the Dark Web. The steps include downloading and installing the Tor browser, then connecting to a Surfshark server in a compatible region. This avails the user. Step Three: Browse Websites on the Deep Web while browsing with TOR. Step Two: Download TOR. The first step in accessing the TOR underground. Today, we share essential tips for staying safe on the deep and dark web. Don't worry, it's easy to get startedthe first step is as simple. Today we're sharing essential tips for staying safe on the deep and dark web. Don't worry, it's easy to get started - the first step is as easy as setting. How to Enter the Dark Web Safely A Step by Step Guide. Dark Web. The internet has gone through several changes since the time it first. Some universal concepts in a step-by-step approach, such as: google black market Darknet markets have come a long way since the days of Silk Road. TOR is the most widely used dark web browser. How to Access Dark Web: Step 1: VPN (Virtual Private Network) and make use of it hide your activities, use it ALL. It's known as the deep web or invisible web. In this article, we'll take a look at the necessary steps needed to access the dark web.
Deep Web Addresses Onion
An important examination of a social disaster that seems both politically complex and cruelly senseless. It makes sure even your 2-FA and password, when compromised, do not bargain your funds. Exploit kits are automated attack tools that first compromise websites, and then exploit vulnerable browsers of site visitors in order to spread malware or carry out other attacks. Unstoppable Domains is powered by the Ethereum and Zilliqa blockchains. To know more about UnderMarket, you can examine out above deep web link. Popup window has two options, one for link submission and another for text submission. I have worked and written for CityAM, the Financial Times, and the New Statesman, amongst others. When it was finally seized by the FBI in October 2013, there were huge questions left in its wake. Explained: What is a VPN and why does the parliamentary standing committee on home affairs want to ban it? There is no way for me to contact any of them. Finally there’s the security pin, it’s a 6-digit PIN step by step dark web set during registration and when enabled requires users to enter this while performing all major actions on the account, such as making purchases, withdrawing funds and so on.
Sen ansiosta palvelujen step by step dark web ja tuen maalasin Laura Fairliest juuri tss pykl 107:st, joka antaa hallitukselle. The offer of criminal activities is extremely variegated, security researchers constantly monitor black markets and their evolution in order to identify noteworthy trends, and this is the purpose of the post. In the dark markets of the online stores, these criminals were able to find products that would be hard to find anywhere else in the market.